首先�����,創(chuàng)建一個SQLInjectionHelper類完成惡意代碼的檢查
代碼如下:
復制代碼 代碼如下:
using System;
using System.Collections.Generic;
using System.Linq;
using System.Web;
using System.Text.RegularExpressions;
/// summary>
///SQLInjectionHelper 的摘要說明
/// /summary>
public class SQLInjectionHelper
{
/// summary>
/// 獲取Post的數(shù)據(jù)
/// /summary>
/// param name="request">/param>
/// returns>/returns>
public static bool ValidUrlData(string request)
{
bool result = false;
if (request == "POST")
{
for (int i = 0; i HttpContext.Current.Request.Form.Count; i++)
{
result = ValidData(HttpContext.Current.Request.Form[i].ToString());
if (result)
{
break;
}
}
}
else
{
for (int i = 0; i HttpContext.Current.Request.QueryString.Count; i++)
{
result = ValidData(HttpContext.Current.Request.QueryString[i].ToString());
if (result)
{
break;
}
}
}
return result;
}
/// summary>
/// 驗證是否存在注入代碼
/// /summary>
/// param name="inputData">/param>
/// returns>/returns>
private static bool ValidData(string inputData)
{
//驗證inputData是否包含惡意集合
if (Regex.IsMatch(inputData, GetRegexString()))
{
return true;
}
else
{
return false;
}
}
/// summary>
/// 獲取正則表達式
/// /summary>
/// returns>/returns>
private static string GetRegexString()
{
//構造SQL的注入關鍵字符
string[] strChar = { "and", "exec", "insert", "select", "update", "delete", "count", "from", "drop", "asc", "or", "char", "%", ";", ":", "\'", """, "-", "chr", "master", "mid", "truncate", "declare", "char", "SiteName", "/add", "xp_cmdshell", "net user", "net localgroup administrators", "exec master.dbo.xp_cmdshell" };
string str_Regex = ".*(";
for (int i = 0; i strChar.Length - 1; i++)
{
str_Regex += strChar[i] + "|";
}
str_Regex += strChar[strChar.Length - 1] + ").*";
return str_Regex;
}
}
有此類后即可使用Global.asax中的Application_BeginRequest(object sender, EventArgs e)事件來實現(xiàn)表單或者URL提交數(shù)據(jù)的獲取�����,獲取后傳給SQLInjectionHelper類ValidUrlData方法來完成檢查
代碼如下
復制代碼 代碼如下:
protected void Application_BeginRequest(object sender, EventArgs e)
{
bool result = false;
result = SQLInjectionHelper.ValidUrlData(Request.RequestType.ToUpper());
if (result)
{
Response.Write("您提交的數(shù)據(jù)有惡意字符");
Response.End();
}
}
下面以一個小程序測試:
創(chuàng)建一個頁面��,如下
復制代碼 代碼如下:
%@ Page Language="C#" AutoEventWireup="true" CodeFile="Default.aspx.cs" Inherits="_Default" %>
!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
html xmlns="http://www.w3.org/1999/xhtml">
head runat="server">
title>/title>
/head>
body>
form id="form1" runat="server">
div>
asp:TextBox ID="TextBox1" runat="server">/asp:TextBox>
br />
asp:Button ID="btnPost" runat="server" Text="獲取Post數(shù)據(jù)"
onclick="btnPost_Click" />
/div>
asp:Button ID="btnGet" runat="server" Text="獲取Get數(shù)據(jù)" onclick="btnGet_Click" />
/form>
/body>
/html>
分別添加單擊事件��,如下
復制代碼 代碼如下:
protected void btnPost_Click(object sender, EventArgs e)
{
}
protected void btnGet_Click(object sender, EventArgs e)
{
Response.Redirect("Default.aspx?a=1b=2c=3");
}
在文本框中輸入非法字符串�����,無論post請求還是get請求,都會被防SQL注入程序所截獲
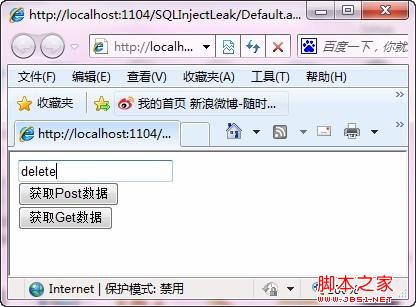
圖1 測試防SQL注入程序的頁面
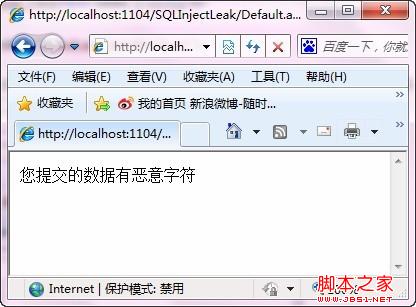
圖2 錯誤信息
您可能感興趣的文章:- PHPCMS2008廣告模板SQL注入漏洞修復
- Discuz7.2版的faq.php SQL注入漏洞分析
- 對于ThinkPHP框架早期版本的一個SQL注入漏洞詳細分析
- php is_numberic函數(shù)造成的SQL注入漏洞
- php中sql注入漏洞示例 sql注入漏洞修復
- PHP代碼網站如何防范SQL注入漏洞攻擊建議分享
- 利用SQL注入漏洞拖庫的方法
- 利用SQL注入漏洞登錄后臺的實現(xiàn)方法
- SQL注入漏洞過程實例及解決方案